Local-first by default
No telemetry, no default network calls, no cloud dashboard, and no live config mutation.
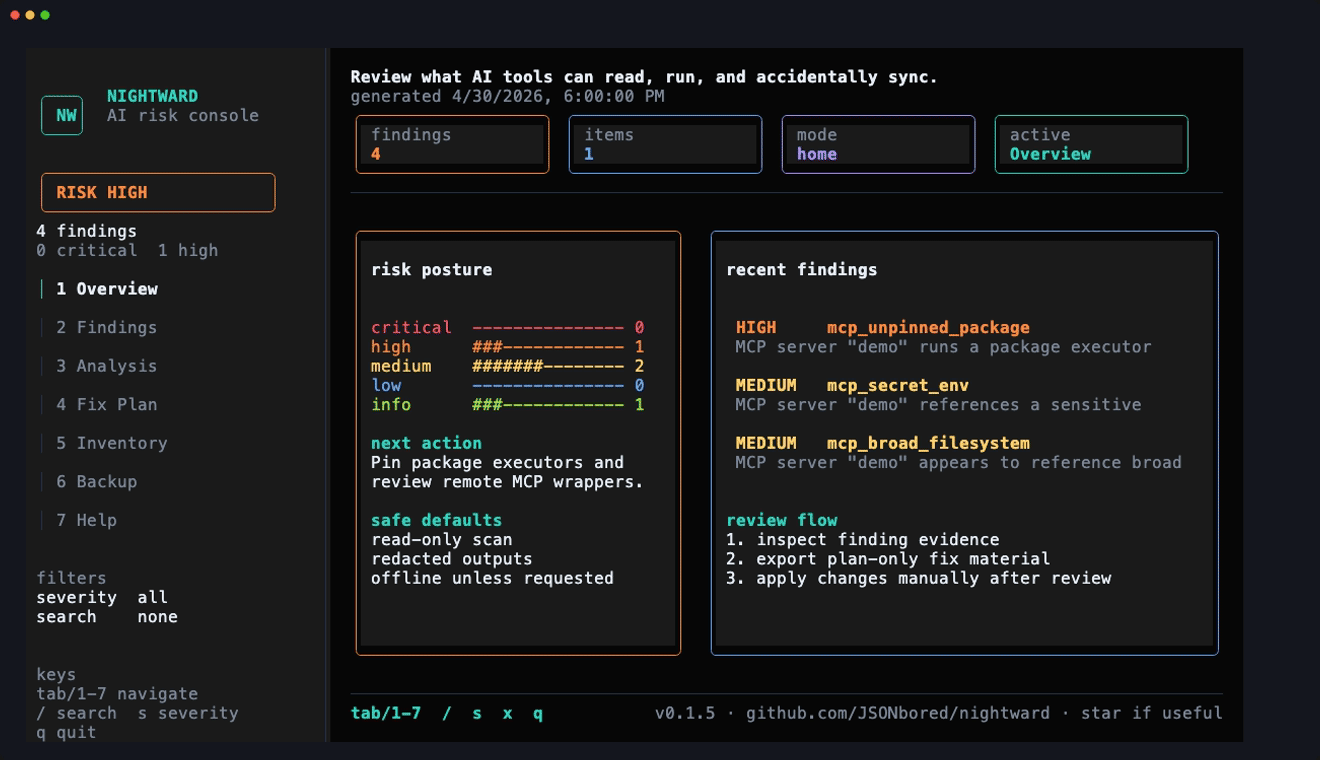
Scan agent configs, MCP servers, and dotfiles for secrets, broad local access, and machine-only state. Local by default. Review-first by design.
Start now
No account, no telemetry, no default network calls, and no config mutation.
npx @jsonbored/nightward scanPrefer a persistent CLI? Use npm, GitHub Releases, or a source build, then run nw.
The sample report below is generated from the committed testdata/homes/policy fixture home. Hostname, HOME, local paths, timestamps, and secret-looking fixture values are scrubbed before publication.
Sample scan JSON · Static HTML report · OpenTUI gallery · OpenTUI GIF · Provider reference · Output surfaces
Terminal review flow
The loop uses the scrubbed fixture report: overview, findings, offline analysis, plan-only fixes, inventory, backup choices, and safety reminders.
| Area | What you get |
|---|---|
| Inventory | Portable, machine-local, secret-auth, runtime-cache, app-owned, and unknown state across HOME or a workspace. |
| MCP security | Findings for unpinned package executors, shell wrappers, broad filesystem mounts, sensitive env/header exposure, local endpoints, token paths, symlinks, parse failures, and unknown server shapes. |
| Report history | Compare scan JSON files, inspect latest-report status, render filterable diff-aware HTML, and generate a static local report index. |
| Policy and CI | Reason-required ignores, policy badges, SARIF output, GitHub Action mode, and Trunk plugin support. |
| Providers | Local Gitleaks, TruffleHog, and Semgrep; online-gated Trivy, OSV-Scanner, and remote Socket scan creation. |
| MCP server | Read-only stdio tools/resources for local AI clients; no network listener, no mutation tools, and no online providers in v1. |
Nightward ships through signed GitHub Releases and a no-postinstall npm launcher that verifies GitHub Release checksums before running a cached Rust binary. The project keeps OpenSSF evidence in-repo, runs CodeQL/Scorecard/Gitleaks/OSV/Clippy, and keeps online-capable providers blocked until explicitly enabled.
Nightward does not copy secrets, push to Git, restore configs, sync machines, or apply live mutations in v1.